From prerequisite to central guiding role
Information security within municipalities
Information security is now part of almost all activities within organizations. It is no longer a vague prerequisite, but steering in planning and execution. Giving this form is proving to be a tough challenge. This is especially true for municipal organizations. Within these decentralized organizations, diverse disciplines work with a wide variety of information systems.
CISOs, FGs and other specialists involved have their hands full in bringing about the change. The current situation: information security is seen as a precondition, which often has to be filled in at the end of a project. The desired situation: information security has a central and guiding role within the organization.
EXTENSIVE, COMPLEX AND CHANGING
Many municipalities have a decentralized form of organization with a large amount and variety of information systems. This requires accountability for security in an almost continuous audit cycle. The context is also constantly changing: after ENSIA and AVG, the BIO is introduced from 2019 and already updated to version 2.0. All these factors make organizing the right information security a complex matter. Here, CISOs and FGs are simultaneously playing chess on multiple boards to achieve consistent and effective information security and privacy protection. Essential here is having an overview and insight.
Having overview and insight is essential to getting in-control of information security within any organization.
Overview: What information systems do we have and what is the "value" of this information to all stakeholders (data classification)? What audits are planned and when should policies be reviewed?
Insight: What risks are there with respect to these information (systems) and how do we take prioritized measures for this? How effective are the existing measures and to what extent do we meet the required standards?
Structure and overview offer insight
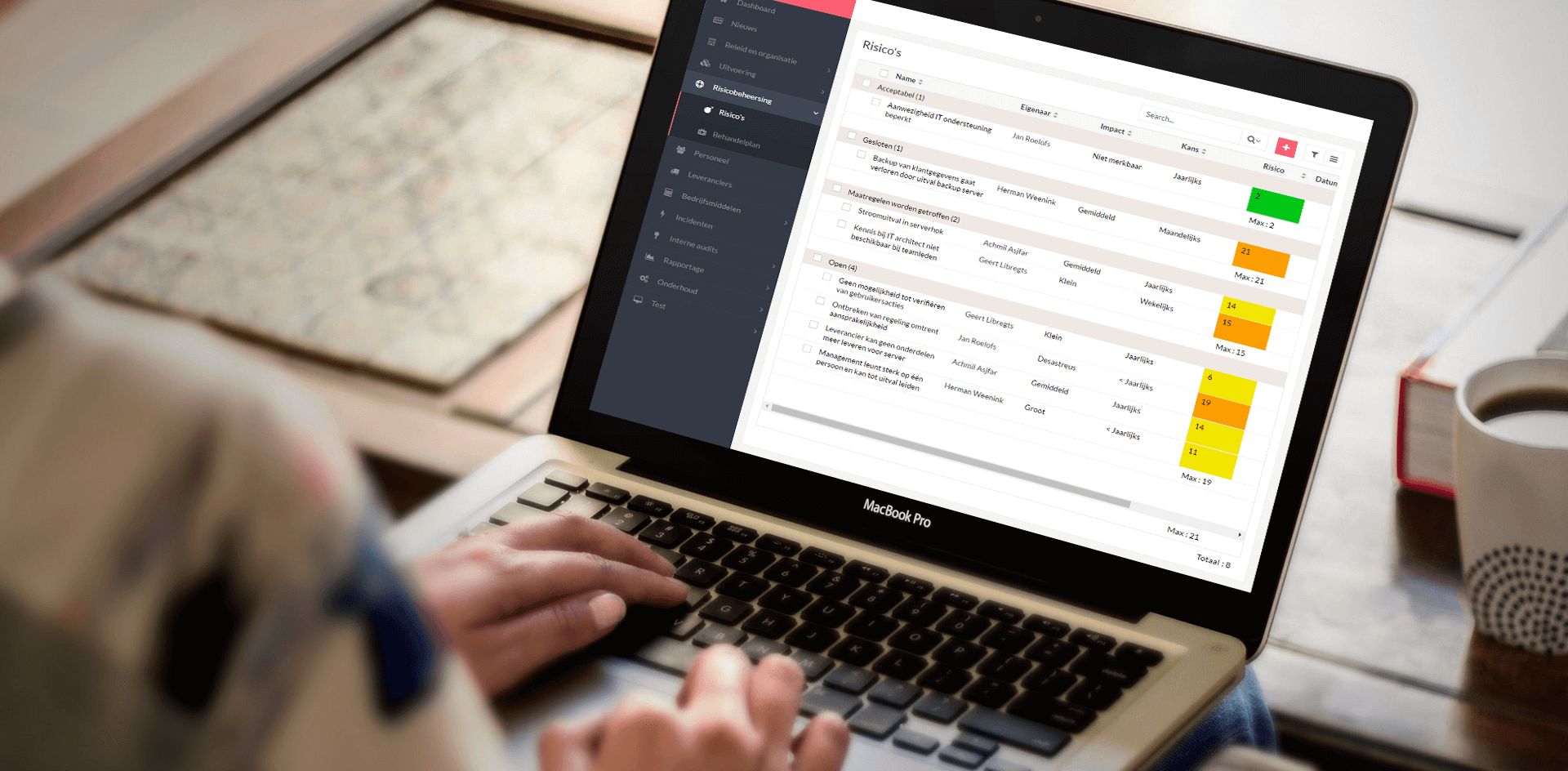
With Base27, Axxemble offers a solution that helps address these issues in a practical way that includes:
- A customized solution to establish, communicate and maintain policies. The associated PDCA cycle is fully supported within this ISMS.
- A module for managing information systems in which all essential parameters, including organization-specific characteristics, can be recorded and from which insight is gained about the status and effectiveness of information security.
- A structured planning of internal controls and external audits. At the push of a button, all necessary information is available for required accountability and management reporting.
- A complete privacy management system including processing log, data breach registration and handling of concerned requests.
- Support for standards frameworks such as the BIG (soon to be the BIO), AVG and, for example, ISO 27001. Insight into progress and relationship with policies and measures is available up to date.
Collaboration
Base27 allows all parties - CISO, FG, IT specialists and end users - to work together in a simple and user-friendly way. The overview and insight achieved will allow the central and guiding role of information security to be fulfilled as a matter of course.
Base27 monitors and registers your processes around information security. It is an ISMS, an information security management system, which gives you a handle on the many and often complex aspects of information security. Base27 supports policy-making, communication, risk analysis, control and registration of assets. Using Base27, you are able to quickly set up information security in accordance with the BIG and ENSIA, including support for the AVG.
The tooling gives you a logical and clear structure in the areas of:

 English
English
 Nederlands
Nederlands